Making cybersecurity matter: tips to justify security spending
Struggling to explain why your team exists? Master three principles to turn security spend into a language executives understand

You already know the story: you spend months on calls, spreadsheets and management pitches. Then - finally - your cybersecurity budget gets approved! Eager to make an impact, you start deploying all the tools you fought so hard to get. Then, the moment invoices start coming through, the dreaded email from the CFO arrives: "Can you remind me why we’re spending this much on this tool?"
Again, you invest hours into explaining why these tools are essential. You know your team depends on them to detect threats, respond to incidents and keep the company out of headlines. But when you try to explain their value, you’re met with blank stares or polite nods before being asked to quickly move on.
Need a field-tested budgeting tool that your CFO can understand? By subscribing to Premium, you can download Blog on Security’s yearly budgeting tool whenever you want.
Fortunately, this isn’t a failure: it’s actually an opportunity. That awkward silence when you mention "threat intelligence feeds" or "attack surface reduction" isn’t a sign of disinterest. It’s a signal that your security team isn’t speaking the same language as the business.
Within that translation gap hides your chance to build credibility, influence and trust with management. CISOs who thrive in this moment don’t just defend their spending; they reframe it as an investment in the company’s growth.
This is easier to achieve than you might think. There are three proven principles that will help you build a fluid funding conversation with management:
- You need to build a budget that your management understands
- You need to link every dollar spent to reduced risks
- You need to show how security is a revenue enabler
In this post, we break down how to apply these principles in practice.
Build a budget that management understands
You can’t justify what you can’t explain. If your cybersecurity funds live embedded into a wider IT budget and only surface through a maze of ad-hoc invoices, surprise IT purchases and "miscellaneous" expense requests, you’ve already lost. Without a centralized, transparent overview of where money goes - and why - security spending will be a black box. And CFOs don't like spending black boxes.
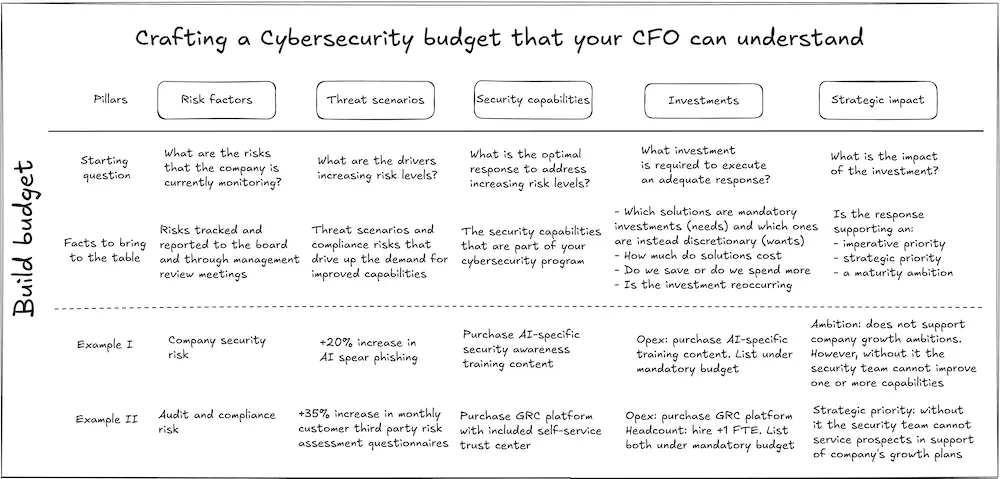
Moreover, simply tracking your spending is not the solution: you need to create a shared language. Your budget should answer three questions for any stakeholder:
- How much are we spending?
- What are we spending it on?
- Why does it matter?
Without this, you will continually face a challenging uphill battle. Even worse, you might leave money on the table. Future legitimate needs can get denied funding simply because their requests were buried in a larger IT budget or lumped under "operational costs." If leadership can’t see your security spend, they can’t value it.
But what if you don't have a dedicated budget? Where do you start? This is a common challenge. In fact, a quick LinkedIn search reveals a recurring complaint: CISOs without a budget have no influence. That’s true, but only up to a point.
Many security leaders don’t control a dedicated budget, especially in smaller organizations. If you are among these, you are not powerless. Instead of fighting for a standalone security budget (which can take years), start by clearly identifying your needs within the existing IT budget and claim your slice. For example:
- Within the IT budget: allocate a percentage to security tools. For example, you can mark 10% of cloud spend as going into security logging.
- Within the compliance budget: tie security initiatives to regulatory requirements. For example, you can say "GDPR fines cost 4% of global revenue; we’re avoiding them by spending A, B, C on initiatives X, Y, Z".
- Within Product budget: mark security costs into feature development. For example, if a new piece of infrastructure requires a Privileged Access Management solution, you should mark the relevant line item within the budget.
The key here is to protect your funding by making it part of larger, business-critical budgets. This approach also forces collaboration with other leaders, which builds alliances and makes future funding requests easier. So how do you build a budget that actually works?
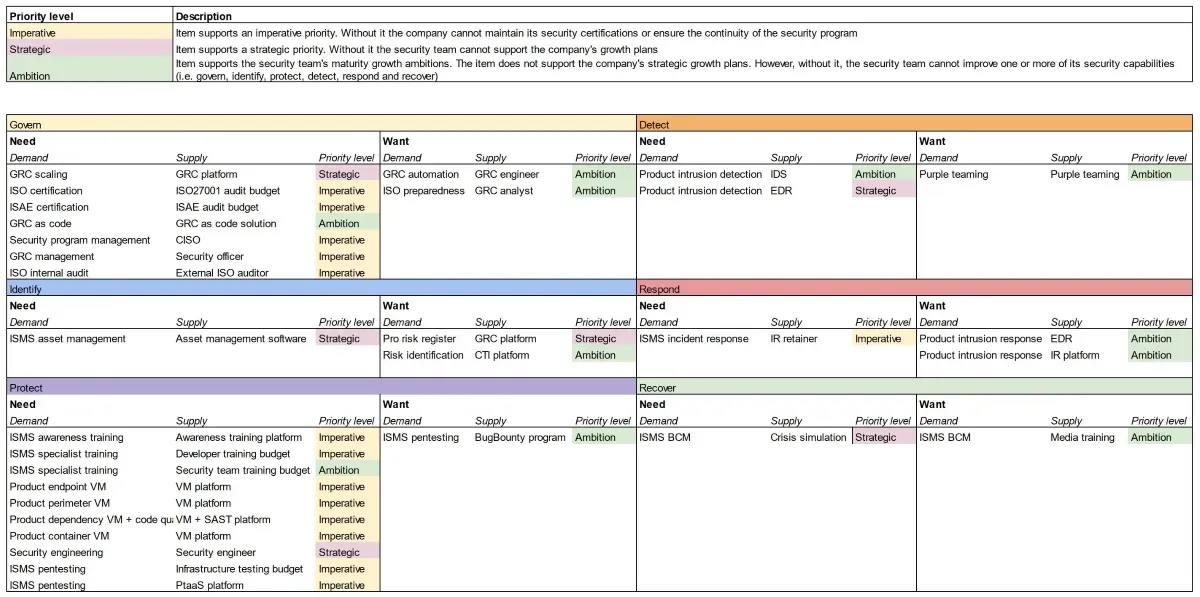
You don’t need complex financial models. You can start with a few simple steps! First, categorize your spending by "supply" and "demand":
- Supply represents your team’s capacity: salaries, training and tools
- Demand represents the initiatives driving your spending: for example, reducing phishing risk, meeting SOC 2 requirements, or responding to incidents
Use a simple tool to track this. A shared spreadsheet works fine for most teams. For each line item, make sure to answer:
- What problem does this solve?
- What happens if we don’t spend this money?
Remember to include a small buffer for unplanned incidents. Typically, 10% of your total budget should do. When something unexpected happens, you’ll be glad you did. Just make sure to be transparent with management about this buffer and clearly articulate the reason for its existence.
Present your budget as a story, not just numbers. For example: "Last year, we spent $80,000 responding to incidents because we lacked proper threat intelligence. This year, we’re investing $30,000 in tool X to cut that cost in half and free up the team for proactive work."
Link security spend to managed risk
Once you have your budget clearly defined, you need to connect every dollar to a tangible risk. However, this is where most security teams naturally hit a wall. A typical strategy is to say, "We need $20,000 for a new EDR tool because the old one doesn’t cut it anymore". The trouble is that this strategy can leave executives wondering, "So what?". Another strategy is to lean on threat intelligence. Specifically, leveraging warnings about the latest headline campaigns or APT groups.
Both approaches can work one-off. However, in the long term, they fall flat because they fail to answer the key question leadership cares about: "How does this impact our business?" Without that bridge, all they hear is "Trust us, it’s important/urgent right now", and that’s not a compelling argument. It eventually runs out of steam.
The more sustainable solution is to anchor your spending to your risk register. For each initiative, you need to be asking:
- Which risk does this mitigate?
- What’s the business impact if we don’t address this risk?
Here’s how this looks in practice:
| Initiative | Risk Mitigated | Business Impact | Cost |
|---|---|---|---|
| Hire security engineer | Unprotected customer databases | $2M in fines | $120K |
| Cyber insurance | High incident response costs | $500K in downtime | $50K |
Putting everything together, you should end up with a budget inventory that connects everything together: capturing risks that drive demand for security initiatives, which in turn are tied to specific budget items.
This approach works because it translates technical needs into business outcomes. For example, Endpoint Detection and Response software stops being "yet another security tool" and becomes "a strategic tool reducing our risk of a $1 million ransomware payout." It also creates accountability: if a risk materializes, you can point to where you flagged it.
What if you don’t have a formal risk register? Use your budget as a starting point. Every line item implies a risk you’re addressing. For example: "We’re spending $15,000 on database encryption because unprotected customer data is one of our top risks. Here’s how we’re fixing it."
This does two important things:
- It educates leadership about risks they might not see
- It positions you as a strategic partner, not just a cost center
Even if management underestimates your warnings, you’ve created a record. If something goes wrong, you can say "We identified this risk in Q1 and proposed a solution. Here’s what happened when we didn’t act." Note that this isn’t about saying "I told you so" or creating "gotcha" moments; it’s about building credibility for future discussions.
Show how security enables revenue
Most security teams get stuck in the "cost center" mindset. This is a natural consequence when teams are stuck in firefighting and are absorbed on avoiding bad outcomes. While these are absolutely critical goals, from a business standpoint they are not enough. To truly justify your spending, you need to show how security helps the company make or save money.
The approach entirely depends on your company's business model. It's very difficult to provide a generalized suggestion that works for every firm out there. However, we can explore two examples that, hopefully, provide sufficient inspiration. For SaaS companies, security directly enables sales. For others, it’s about cost avoidance. Let’s look at both:
SaaS and service companies: security as a sales enabler
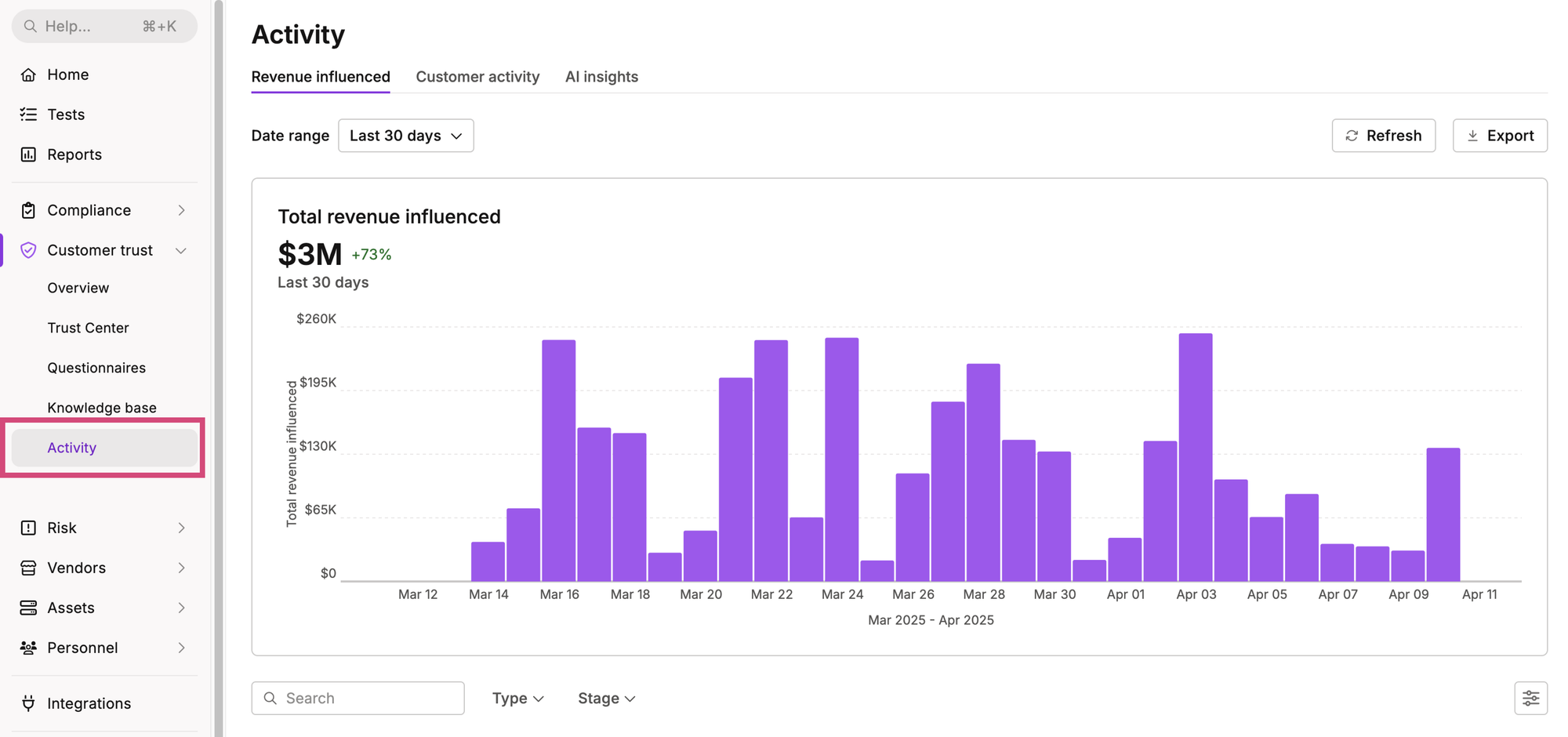
If your company sells to other businesses, especially in regulated industries, security is a revenue driver. To prove it, you can work with your sales team to track deals where security was an influencing factor. Influencing factors encompass activities such as responding to security questionnaires, contributing to pre-sales engineering activities, participating in calls to answer security and regulatory concerns, etc.
The important thing is aligning with sales and management on the definition of "security sales contributions". Once that is done, you need to track them. Many CRM tools let you tag deals with "security questionnaire completed" or similar markers. Even better, some GRC tools like Vanta even integrate with Salesforce to automatically track this for you.
Once you have all of this in place, calculating the security return on investment should be fairly easy:
- Total revenue from deals where security was a factor: $Y
- Total security team cost: $Z
- If Y > Z, you’re generating more value than you cost
For example: "Our security team contributed to $1.2 million in closed deals last year at a cost of $300,000. That’s a 4:1 return on investment."
That's a very powerful position to be in and it completely shifts the conversation away from cost center concerns. More importantly, you can ask for a share of the winnings by making a strong case: "We helped win $1.2 million in deals. Can we reinvest 10% to scale our security efforts?"
For other industries: benchmarking for cost savings
If you can’t tie security directly to sales, you can focus on cost avoidance that - ultimately - leads to more revenue. Working with your cyber insurance provider can be a winning strategy. Start by asking them for:
- Your premium vs. industry average
- Common claims (in dollar value) for your sector
Then show the difference: "Our premium is 20% below average because of our security maturity. That’s $50,000 saved annually."
You can then frame it as money kept in the business: "We’re not just spending $200,000 on security: we’re bringing $250,000 back to the bottom line by avoiding breaches and lowering insurance costs."
From cost center to strategic partner
When you apply these three principles correctly, you should see the following:
- A reduction in the number of times management asks for reminders or justifications on security spend, therefore less time spent answering these repetitive concerns
- You break out of a narrow focus on security strategy and are invited to wider strategic discussions concerning the business
- Security starts to be seen as a value driver, not just a "cost of doing business"
Remember, the goal isn’t just to justify spending. Rather, it’s to make cybersecurity matter to the business. When you connect security to risk management and revenue, you build a program that the company can’t afford to ignore.